Add a Trusted Device
When you become a member of an organization, the device you log in with for the first time will automatically be registered as a trusted device. Once this occurs, all you'll need to do to log in to Bitwarden and decrypt your data is complete your company's established single sign-on flow.
tip
Devices will be trusted by default when you log in on them. It is highly recommended that you uncheck the Remember this device option when logging in on a public or shared device.
When you log into a new device however, you'll need to approve, or trust, that device. There are a few methods for doing so:
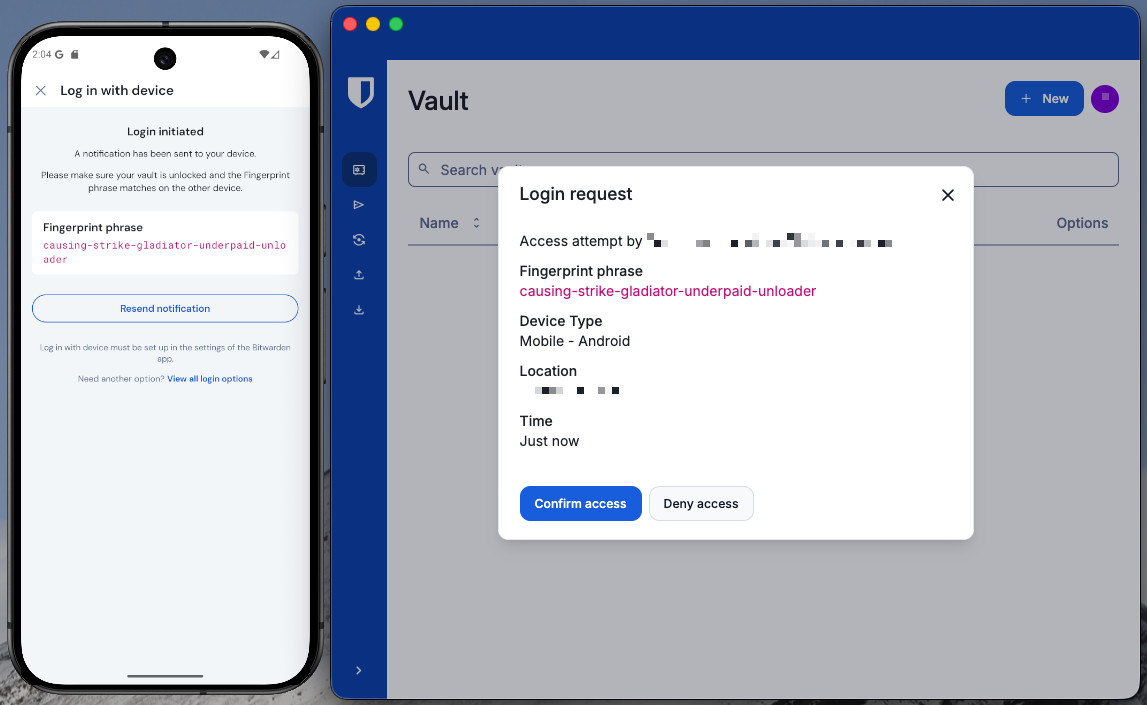
Approve from another device: If you're already logged into Bitwarden on another device, you can approve the new device from there:
To approve a request with the mobile app:
In the mobile app, navigate to Settings → Account security → Pending login requests:

Pending login requests on mobile Locate and tap the pending device request.
Verify that fingerprint phrase matches and select Confirm access:

Approve a login on mobile
Use master password: If you are an admin or owner, or joined your organization before SSO with trusted devices was implemented, and therefore still have a master password associated with your account, you can enter it to approve the device.

Request admin approval Request admin approval: You can send a device approval request to admins and owners within your organization for approval. You must be enrolled in account recovery to request admin approval, though you may have been automatically enrolled when you joined the organization. In many cases, this will be the only option available to you (learn more).
note
If you use this option, you'll get an email informing you to continue logging in on the new device when you're approved. You must take action by logging in to the new device within 12 hours, or the approval will expire.
Once the new device becomes trusted, all you'll need to do to log in to Bitwarden and decrypt your vault data is complete your company's established single sign-on flow.
Adding your first trusted device
The initial client used to access Bitwarden for users who were invited with Just in Time (JIT) provisioning using login with SSO will become their first trusted device. If the initial client accessed is the Bitwarden desktop or mobile app, this device can be used to approve additional devices.
For the desktop or mobile app to become the first trusted device, the user should not use the organization invite link. Instead, open the mobile or desktop app and select the Enterprise single sign-on option to begin the JIT process.
Remove a trusted device
Devices will remain trusted until:
The application or extension is uninstalled.
The web browser's memory is cleared (web app only).
Troubleshooting
If you're having trouble establishing device trust:
On Chrome, check that Allow sites to save data on your device is turned on (Settings → Privacy and security → Site settings → Additional content settings → On-device site data → Allow sites to save data on your device).