Om betrodda enheter
SSO med betrodda enheter tillåter användare att autentisera med SSO och dekryptera sitt valv med en enhetslagrad krypteringsnyckel, vilket eliminerar behovet av att ange ett huvudlösenord. Betrodda enheter måste antingen registreras före inloggningsförsöket eller godkännas genom några olika metoder.
SSO med betrodda enheter ger affärsslutanvändare en lösenordslös upplevelse som också är noll-kunskap och krypterad från början. Detta förhindrar användare från att bli utelåsta på grund av glömda huvudlösenord och låter dem njuta av en strömlinjeformad inloggningsupplevelse.
Börja använda betrodda enheter
Så här kommer du igång med SSO med betrodda enheter:
Konfigurera SSO med betrodda enheter för din organisation.
Ge administratörer information om hur de godkänner enhetsbegäranden.
Ge slutanvändare information om hur man lägger till betrodda enheter.
Hur det fungerar
Följande flikar beskriver krypteringsprocesser och nyckelutbyten som sker under olika procedurer för betrodda enheter:
När en ny användare går med i en organisation skapas en kontoåterställningsnyckel (läs mer) genom att kryptera deras kontokrypteringsnyckel med organisationens offentliga nyckel. Kontoåterställning krävs för att aktivera SSO med betrodda enheter.
Användaren tillfrågas sedan om de vill komma ihåg, eller lita på, enheten. När de väljer att göra det:
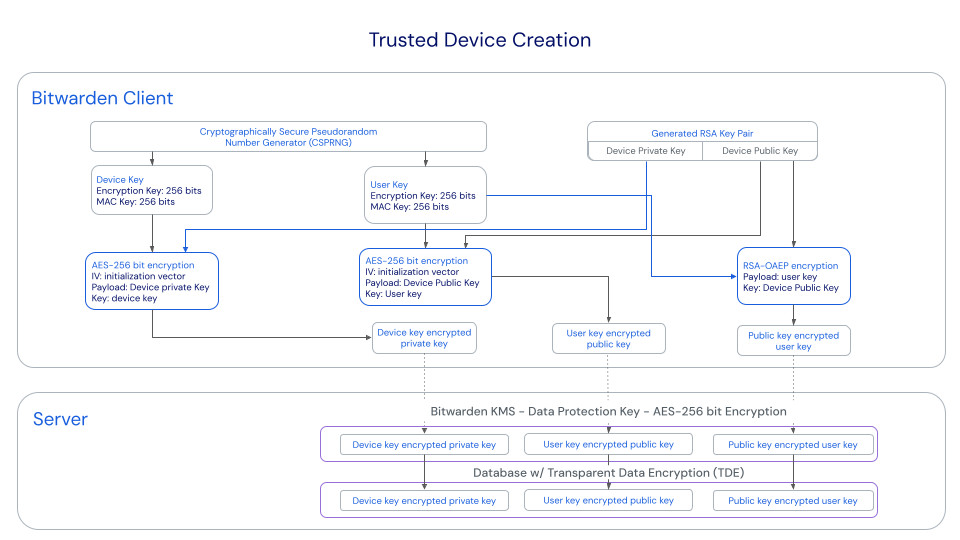
En ny enhetsnyckel genereras av klienten. Denna nyckel lämnar aldrig klienten.
Ett nytt RSA-nyckelpar, kallat Device Private Key och Device Public Key, genereras av klienten.
Användarens kontokrypteringsnyckel krypteras med den okrypterade enhetens publika nyckel och det resulterande värdet skickas till servern som den offentliga nyckelkrypterade användarnyckeln.
Den offentliga enhetens nyckel krypteras med användarens kontokrypteringsnyckel och det resulterande värdet skickas till servern som den användarnyckelkrypterade publika nyckeln.
Enhetens privata nyckel krypteras med den första enhetsnyckeln och det resulterande värdet skickas till servern som den enhetsnyckelkrypterade privata nyckeln.
Den offentliga nyckel-krypterade användarnyckeln och enhetsnyckel-krypterade privata nyckel kommer, avgörande, att skickas från server till klient när en inloggning initieras.
Den användarnyckel-krypterade publika nyckeln kommer att användas om användaren behöver rotera sin kontokrypteringsnyckel.
Nycklar som används för betrodda enheter
Den här tabellen ger mer information om varje nyckel som används i procedurerna som beskrivs ovan:
Nyckel | Detaljer |
|---|---|
Enhetsnyckel | AES-256 CBC HMAC SHA-256, 512 bitars längd (256 bitar för nyckel, 256 bitar för HMAC) |
Enhetens privata nyckel och enhetens offentliga nyckel | RSA-2048 OAEP SHA1, 2048 bitars längd |
Public Key-krypterad användarnyckel | RSA-2048 OAEP SHA1 |
Användarnyckel-krypterad offentlig nyckel | AES-256 CBC HMAC SHA-256 |
Enhetsnyckel-krypterad privat nyckel | AES-256 CBC HMAC SHA-256 |
Inverkan på huvudlösenord
Även om SSO med betrodda enheter eliminerar behovet av ett huvudlösenord, eliminerar det inte i alla fall själva huvudlösenordet:
Om en användare är ombord innan SSO med betrodda enheter aktiveras, kommer deras konto att behålla sitt huvudlösenord.
Om en användare är ombord efter att SSO med betrodda enheter har aktiverats och de väljer Logga in → Enterprise SSO från organisationens inbjudan för JIT-provisionering, kommer deras konto inte att ha ett huvudlösenord. Om du byter till dekrypteringsalternativet för huvudlösenord kommer dessa användare att uppmanas att skapa ett huvudlösenord när de loggar in så länge de fortfarande är medlem i organisationen (läs mer).
warning
För de konton som inte har huvudlösenord som ett resultat av SSO med betrodda enheter, avbryts all åtkomst till deras Bitwarden-konto om du tar bort dem från din organisation om:
Du tilldelar dem ett huvudlösenord med kontoåterställning i förväg.
Användaren loggar in minst en gång efter kontoåterställning för att fullständigt slutföra arbetsflödet för kontoåterställning.
Dessutom kommer användare inte att kunna gå med i din organisation igen om inte ovanstående steg vidtas innan de tas bort från organisationen. I det här scenariot kommer användaren att behöva ta bort sitt konto och få en ny inbjudan att skapa ett konto och gå med i din organisation.
Att återkalla åtkomst till organisationen, men inte ta bort dem från organisationen, kommer fortfarande att tillåta dem att logga in på Bitwarden och bara komma åt sitt individuella valv.
Om ett användarkonto återställs med kontoåterställning kommer deras konto nödvändigtvis att tilldelas ett huvudlösenord. Ett huvudlösenord kan för närvarande inte tas bort från ett konto när det väl har ett, så för att undvika detta rekommenderar vi att du (i) instruerar användaren att exportera sina data till en säkerhetskopia, (ii) helt radera det förlorade kontot, (iii) ber användaren att återgå till din organisation med hjälp av betrodda enheter och (iv) när de har gjort det instruerar dem att importera sin säkerhetskopia.
Inverkan på andra funktioner
Beroende på om ett huvudlösenords-hash är tillgängligt i minnet för din klient, vilket dikteras av hur din klientapplikation initialt öppnas, kan den uppvisa följande beteendeförändringar:
Särdrag | Inverkan |
|---|---|
Kontroll | Det finns ett antal funktioner i Bitwarden-klientapplikationer som vanligtvis kräver inmatning av ett huvudlösenord för att kunna användas, inklusive export av valvdata, ändring av tvåstegsinloggningsinställningar, hämtning av API-nycklar och mer. Om användaren inte använder ett huvudlösenord för att komma åt klienten kommer alla dessa funktioner att ersätta huvudlösenordsbekräftelse med e-postbaserad TOTP-verifiering. |
Valv låsa/låsa upp | Under vanliga omständigheter kan ett låst valv låsas upp med ett huvudlösenord. Om användaren inte använder ett huvudlösenord för att komma åt klienten, kan låsta klientapplikationer endast låsas upp med en PIN-kod eller med biometri. Om varken PIN eller biometri är aktiverade för en klientapplikation kommer valvet alltid att logga ut istället för att låsa. Upplåsning och inloggning kräver alltid en internetanslutning. |
Uppmaning om huvudlösenord | Om användaren inte låser upp sitt valv med ett huvudlösenord, kommer återuppmaning av huvudlösenordet att inaktiveras. |
Ändra e-postadress | Användare som inte har huvudlösenord kommer inte att kunna ändra sin e-postadress. |
CLI | Användare som inte har huvudlösenord kommer inte att kunna komma åt Password Manager CLI. |
