Bitwarden Send is a trusted method for transmitting encrypted information directly to anyone. When creating a new Send, users can set up password fields and options for expiring messages after they've been accessed, ensuring user security and ease of use during the creation process.
Introduction to secure sharing
It’s crucial to be able to share sensitive information securely. This is where Bitwarden Send comes into play. Bitwarden Send enables users to securely share sensitive data, including passwords and files, in an encrypted manner.
Using end-to-end encryption, Bitwarden Send ensures that only the intended recipient can access the shared information. This means that your data is protected from prying eyes at every stage of the transmission process. Whether you are sharing financial data, personally identifiable information, or any other sensitive information, Bitwarden Send provides a secure solution that you can trust.
For individuals and organizations alike, Bitwarden Send offers peace of mind. You can share sensitive information with confidence, knowing that robust encryption protocols protect your data.
Getting started with Bitwarden Send
Getting started with Bitwarden Send is a straightforward process. First, create a Bitwarden account and install the Bitwarden app on your device. Once you have installed the app, accessing the Send feature is simple. Click on the Send icon within the app to begin. From there, you can create a new Send by selecting the file or text you want to share.
Security with Bitwarden Send
Similar to all of your Bitwarden vault data, everything shared through Bitwarden Send is end-to-end encrypted. This means that Bitwarden cannot see the contents of your Send, whether that be a text snippet or a file.
One of the important components of Bitwarden Send is built-in automatic deletion. Because the sensitive data will be automatically deleted within a specified timeframe, users can ensure their information does not linger or remain in a system over which they have no control. For example, in a typical sharing model, once a piece of information is emailed or messaged, it stays in those systems often forever. Using the Bitwarden end-to-end security model, while the Send link may remain, it will no longer function, and the data attached to that Send will be deleted. This feature ensures that only the intended recipients can access the shared information.
A Bitwarden Send link can be further protected with user-configured parameters, including:
A deletion date when the Send is permanently deleted
An expiration date when the Send link is no longer active, but remains in your Vault (available in web and desktop apps only)
A maximum access count, after which users will no longer have access. Maximum access counts limit prying eyes that might not otherwise need access to the information.
An optional password is required to access the Send
A disable option, so that no one can access the Send if selected
Understanding a Bitwarden Send link
A Bitwarden Send link might display like the following:
https://send.bitwarden.com/#mS2LfeyK3xn3fVEQXzYnnh/Hayk8N7x792Ydx3wYD4cPf
After the hash (#), the Send ID appears, and then after the forward slash (/) is the Send encryption key.
It is important to note that:
The Bitwarden Send link is generated client-side and not on the Bitwarden server, so Bitwarden can never see the content of the Send.
The link contains full access to the Send.
If someone were to get the link, they could access and decrypt the Send while the link is still active, unless the Send is also protected with a password.
Transmitting a Bitwarden Send link
It is normal to ask, “Why is it safe to transmit a Bitwarden Send link through insecure channels?”
First, end-to-end encryption ensures that Bitwarden as a service can never see the contents of your Send. In other words, Bitwarden has zero knowledge of your Send contents.
Second, if you password-protect your Bitwarden Send, communicate that password to the recipient through a different channel. It doesn’t matter whether the main Send channel you use is secure, because your Send cannot be accessed by anyone or anything except the recipient.
It’s essential to note that if you don’t password-protect your Bitwarden Send and transmit the Send link through a channel that could be compromised, your Send may also be at risk. That said, you have the option to limit the time when the Send is active by setting an expiration or deletion time and date. Or, of course, simply add a password and transmit that through a different channel. For example, you could transmit the Bitwarden Send link through email, and use a messaging service, voice call, or SMS to share the password.
Finally, by design, every Bitwarden Send link becomes inaccessible to users after a specified period of time. So, if your email is secure at the time of transmission but later exposed to a hack, a Send with a short deletion window will not be available to be uncovered, and your Send link will not be exposed.
Technical details of Bitwarden Send passwords and keys
The Send password, added optionally to each individual Send, is completely distinct from the Send key used for data encryption.
The Send password is user-defined, optional, and a basis for authentication on an individual Send. Users can click on a Send listing to edit its options, such as adding or changing the password protection and setting expiration settings.
The Send key, which facilitates the Bitwarden encryption and decryption of the Send data, is auto-generated and required for Send use.
Anatomy of a URL
The Mozilla Foundation has a helpful article on understanding the elements of a URL. Most important is the identification and explanation of the Anchor (or hash/fragment), and how that is treated.

It is worth noting that the part after the #, also known as the fragment identifier, is never sent to the server with the request. - Mozilla.org
Anatomy of a Bitwarden Send URL
With a Send URL, we can show the following breakdown. When you click the Send icon in the Bitwarden app, the resulting window allows you to input details for the new Send, including naming the Send and selecting a file to attach.
https://send.bitwarden.com/#mS2LfeyK3xn3fVEQXzYnnhM2unTC/Hayk8N7x792Ydx3wYD4cPfMEBXAU
Protocol
https://
Domain
Anchor/fragment/hash - #SendID/SendKey
#mS2LfeyK3xn3fVEQXzYnnhM2unTC/Hayk8N7x792Ydx3wYD4cPfMEBXAU
Send ID
mS2LfeyK3xn3fVEQXzYnnhM2unTC
Send Key
Hayk8N7x792Ydx3wYD4cPfMEBXAU
The anchor, fragment, or hash is not sent to the server. Instead, this information is used locally within the browser to identify and decrypt the Send.
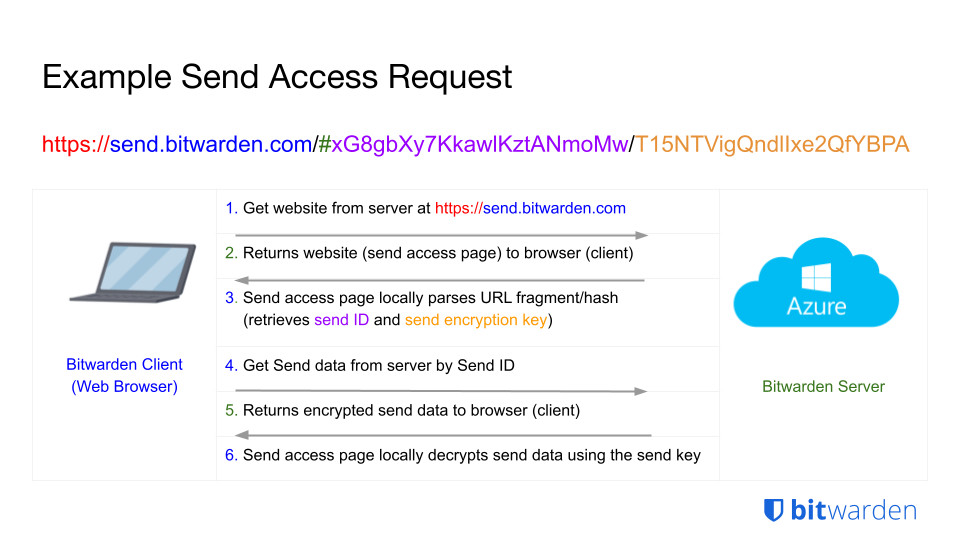
Steps of a Send access request
Let’s explore the steps of a Send request based on this example Send URL:
https://send.bitwarden.com/#mS2LfeyK3xn3fVEQXzYnnhM2unTC/Hayk8N7x792Ydx3wYD4cPfMEBXAU
1. CLIENT
Requests to get the website from the server at https://send.bitwarden.com
2. SERVER
Returns the website of the Send Access Page to the browser client
3. CLIENT
Locally, the Send Access Page parses the URL fragment/hash and retrieves the Send ID (mS2LfeyK3xn3fVEQXzYnnhM2unTC) and the Send Encryption Key (Hayk8N7x792Ydx3wYD4cPfMEBXAU)
4. CLIENT
Requests to get the Send data from the server with the Send ID (mS2LfeyK3xn3fVEQXzYnnhM2unTC)
5. SERVER
Returns the encrypted data for the Send object to the browser CLIENT
6. CLIENT
Locally, the Send Access Page decrypts the Send object using the Send Encryption Key (Hayk8N7x792Ydx3wYD4cPfMEBXAU)
The sequence above is detailed graphically in the image below.
Advanced approaches
For advanced users, an additional method is available that can provide even more protection. Since the Send ID and the Send Encryption Key are part of the anchor and visible in plain text, they can be manually separated and shared through different channels. This method allows for limited access to shared information, enhancing security by restricting the maximum access count or setting an expiry time.
This approach would require the recipient to be familiar with how to handle these pieces of information; therefore, it would be best suited for colleagues who are already familiar with Bitwarden Send.
Additional Bitwarden Send documentation
For Bitwarden Send documentation, please visit the Help Center.
Try Bitwarden Send today
Bitwarden Send is available across all Bitwarden clients, including mobile devices, and text-only Send capabilities are included in a free account. Upgrade to a premium account or enterprise plan to enjoy using Send for text and files, ensuring a smooth and secure experience on all platforms.
