Los administradores de secretos son soluciones de software para gestionar, compartir, almacenar y automatizar secretos de infraestructura a lo largo del ciclo de vida del desarrollo, y desempeñan un papel crucial en la ciberseguridad moderna al prevenir costosas filtraciones de datos. Por lo general, los usan profesionales de DevOps, desarrollo o TI; una funcionalidad clave de los administradores de secretos es facilitar el acceso programático de máquinas a los secretos dentro de un proyecto o tarea de un desarrollador.
Por lo general, los administradores de secretos almacenan secretos como:
Credenciales de autenticación - Nombres de usuario, contraseñas, tokens de API y claves SSH.
Credenciales de base de datos - Cadenas de conexión, nombres de usuario de bases de datos y contraseñas.
Claves de cifrado - Claves usadas para el cifrado y descifrado de datos.
Certificados - Certificados SSL/TLS y claves privadas.
Secretos de configuración de aplicaciones - Variables de entorno, archivos de configuración y secretos específicos de la aplicación.
¿Por qué usar un administrador de secretos?
Seguridad
Los administradores de secretos reducen significativamente el riesgo de filtrar secretos y de exponer potencialmente la infraestructura empresarial al proteger los secretos en un único lugar cifrado. Funcionalidades de seguridad adicionales, como controles de acceso, registros de auditoría y rotación de secretos, también reducen la probabilidad de error humano al trabajar con secretos sensibles.
Eliminar la dispersión de secretos
Debido a que los equipos de desarrollo usan muchos microservicios, aplicaciones y ecosistemas distintos para su trabajo, los secretos críticos pueden distribuirse fácilmente por toda la organización sin una gestión centralizada. Un administrador de secretos ayuda a las organizaciones a gestionar el acceso a estos secretos desde una única fuente de verdad.
Ahorro de costos
Las empresas logran ahorros de costos al usar soluciones de gestión de secretos para abordar de forma proactiva la seguridad de los desarrolladores, en lugar de tomar medidas reactivas después de una filtración de datos. Según Forbes, “se espera que los costos de los daños por ciberdelincuencia a nivel mundial crezcan un 15%” en 2024, “y alcancen los 10.5 billones de USD al año para 2025”. Con un administrador de secretos, las empresas pueden prevenir estos costos de daños asociados con filtraciones relacionadas con credenciales.
Cumplimiento
Ayude a su empresa a cumplir con normativas de protección de datos como ISO/IEC 27001 mediante capacidades detalladas de auditoría y elaboración de informes, proporcionadas por su administrador de secretos.
Productividad de los desarrolladores
Con un administrador de secretos, los equipos de desarrollo ya no necesitan gestionar y proteger secretos de forma manual; en su lugar, pueden recuperar secretos de manera programática. Esto libera más tiempo para mejorar la calidad del código y enfocarse en lo más importante.
El ecosistema de desarrollo
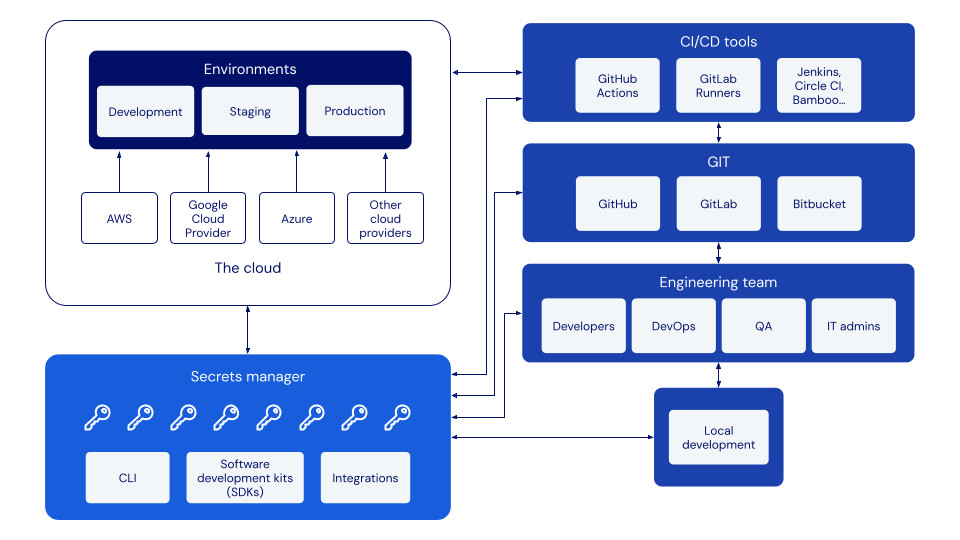
Antes de aprender cómo funciona un administrador de secretos, es importante entender cómo operan los equipos de desarrollo y qué ecosistemas, entornos y herramientas utilizan.
Un ecosistema de desarrollo típico está compuesto por lo siguiente:
Entornos
Los entornos son espacios de trabajo para que los ingenieros construyan sistemas y aplicaciones de software. Los entornos comunes en un ciclo de vida de desarrollo de software incluyen, entre otros, desarrollo, preproducción y producción. Cada entorno requiere un conjunto distinto de secretos para funcionar. Proveedores de nube como Azure, AWS y Google también pueden interactuar con estos entornos para almacenar y compartir datos.
Herramienta(s) de CI/CD
Una canalización de CI/CD (integración continua/entrega continua) se usa para automatizar un proceso de entrega de software y estandarizar los ciclos de retroalimentación. Hay muchas herramientas de CI/CD para elegir que facilitan esta automatización, incluidas GitHub Actions, GitLab Runners, Jenkins, Circle CI, Bamboo y más.
GIT
GIT (global information tracker) es un sistema de control de versiones que se usa a menudo en el desarrollo de software y permite que los ingenieros trabajen simultáneamente en un paquete o proyecto de código fuente. Entre las herramientas populares de GIT se incluyen GitHub, GitLab y Bitbucket.
Desarrollo local
El desarrollo local es el trabajo de desarrollo de software que se realiza en una máquina local (como una computadora u otro dispositivo) antes de enviarlo al código base de un entorno.
Equipo de ingeniería
Una estructura de ingeniería estándar consta de desarrolladores, DevOps, aseguramiento de la calidad (QA) y administradores de TI.
Un Administrador de secretos
Un Administrador de secretos almacenará los secretos necesarios para que estas diversas herramientas, máquinas y proveedores de nube interactúen y se autentiquen entre sí.
Todo el ecosistema
Revise el diagrama a continuación para ver el ecosistema completo de desarrollo.
¿Cómo funciona un Administrador de secretos?
Almacene sus secretos de forma segura
Primero, los secretos se importan o se agregan manualmente a un Administrador de secretos, donde se protegen del acceso no autorizado mediante cifrado. Consejo: elija una solución que usecifrado de extremo a extremo para obtener la mayor seguridad. Una vez agregados los secretos, el Administrador de secretos servirá como la fuente de verdad de su organización para las credenciales de desarrollo e infraestructura.
Restrinja el acceso a empleados y máquinas con privilegios
Luego, asigne permisos de acceso y edición de secretos a los empleados adecuados, como desarrolladores, ingenieros de DevOps y gerentes de TI, siguiendo el principio de privilegio mínimo. En muchos administradores de secretos, los permisos se pueden asignar a grupos de empleados o a empleados individuales para acceder o editar grupos de secretos o secretos individuales. Elija la estructura de permisos que tenga sentido para su empresa y caso de uso.
Asigne permisos de acceso y edición a las máquinas pertinentes, incluidas bases de datos, aplicaciones, sitios web e infraestructuras que interactúan con el o los secretos.
Inyecte secretos en los flujos de trabajo de desarrollo
Por último, se usa un ID de secreto seguro, generado desde el Administrador de secretos, en lugar de un secreto en texto plano en un archivo .env o un script. Si el usuario y la máquina tienen acceso al secreto en cuestión, el valor del secreto se extraerá de forma segura del Administrador de secretos, listo para usarse.

Funcionalidades adicionales incluidas en los administradores de secretos
Los administradores de secretos a veces incluyen funciones y funcionalidades para mayor seguridad y flexibilidad de implementación.
Registros de auditoría- Capture registros con marca de tiempo de todas las acciones de gestión de secretos para investigar actividad potencialmente sospechosa.
Opciones adicionales de autenticación - Además de un nombre de usuario y una contraseña estándar, las opciones de autenticación pueden incluir inicio de sesión único, autenticación de dos factores, claves de acceso, biométrica o integraciones de directorio.
Múltiples opciones de hospedaje - Hospede su solución de gestión de secretos en la nube o en sus propias infraestructuras para mayor control.
Integraciones - Cree fácilmente relaciones entre sus distintas máquinas, canalizaciones de CI/CD, herramientas de automatización y proveedores de nube con integraciones listas para usar.
SDK - Cree operaciones personalizadas con herramientas de desarrollo específicas del lenguaje en un paquete instalable.
Proteja sus secretos de desarrollo e infraestructura con Bitwarden Administrador de secretos
¿Listo para comenzar su proceso de gestión de secretos? Elija el Administrador de secretos con cifrado de extremo a extremo y de código abierto en el que confían equipos y empresas de todos los tamaños para proteger sus secretos críticos: Bitwarden Administrador de secretos.
Bitwarden Administrador de secretos ofrece precios predecibles y almacenamiento ilimitado de secretos en cualquier plan. Para probar toda la funcionalidad empresarial que ofrece Bitwarden Administrador de secretos, regístrese gratis u opte por una prueba empresarial de 7 días para explorar todas las funcionalidades para Empresa que ofrece Bitwarden Administrador de secretos. También puede comunicarse con ventas para una consulta personalizada.

